Human Rights Eroding in the Name of Copyright Protection
By HUNG Chao-Kuei on Sunday, June 6 2010, 11:04 - Permalink
(Invited submission for the Taiwan Branch of The Association of World Citizens.)
Human rights are gradually eroding at several fronts as international interest groups lobby and pressure governments all over the globe to "protect copyright" using big-brother-like information and communication technologies (ICT).
Microsoft's WAT component for Windows 7 validates a user's computer, every 90 days, against its constantly updated database. The motivation looks innocent -- it's just a technical measure deployed against potential piracy. After all, people who respect Microsoft's copyright have no need to worry, right? Yet Microsoft's track record of disrespecting users' fair use right (g: "fairuse4wm controversy") and disrespecting users' will not to upgrade (g: "windows stealthy update") indeed provide reasons for us to be worried. Imagine that a world-wide government installs tiny robots at everybody's home, constantly watching for wrong-doings of your family. And the software of the robots can be remotely upgraded by the government whether you like it or not. If we can accept WAT, we can certainly also accept such invasion of human right and privacy by the government.
Apple's customers cannot exercise their rights over their own physical properties -- the iPhones for which they have paid Apple. Apple forbids its customers to install software programs other than those provided by Apple's iTunes App Store. (g: "eff jailbreak") Imagine buying a house and being forbidden to put any furniture into it except those explicitly allowed by the construction company. If we can accept Apple's control over its customers, we can certainly also accept such invasion of human right by the construction company.
Amazon's Kindle e-book has a piece of software that not only sends user's information back to Amazon but also sends Amazon's commands to Kindle whenever the user connects to its online bookstore WhisperNet. What commands have been sent? Instructions to delete books (with a corresponding refund), for example, in the name of Amazon's respect for the publisher's copyright. (g: "kindle Orwell") Imagine that the Big Brother collects everyone's reading habits and notes as well as deleting any books/articles/forwarded emails that he deems "ungood" and harmful to the society. If we can accept Kindle's remote removal of already-purchased books, we can certainly also accept such invasion of human right and privacy by the Big Brother. Speaking of Big Brother, the books deleted happen to be George Orwell's "1984" and "Animal Farms".
The blu-ray discs employ a complicated but vulnerable DRM (digital rights/restrictions management) encryption system called AACS as a measure of copyright protection. A user who has lawfully bought such a disc and who uses a less popular operating system such as GNU/Linux will receive no supports as to how to play the disc on her system. So such users collaborate to help each other play blu-ray discs on their computers. When a user posted a 16-byte number beginning with "09 F9" on a news site Digg, the AACS Licensing Administrator demanded Digg to take it down. (g: "09 F9 controversy" also search for "09 F9" images) Imagine that a publisher sells you books whose printed words are only readable when you wear their special glasses. You figure out how to bypass this restriction and share your knowledge on the internet, and then the publisher harasses you and the internet forum with legal threats. If we can accept AACS LA's censorship of such a short number, we can certainly also accept such censorship of speech by the publisher.
Can we accept all of these? We already do, even happily paying for the privilege of possessing these beautiful golden handcuffs and diamond leg irons. The Universities are largely silent about these incidents and the damages to human rights that they bring. They have left the education business to the creators of these technologies, and the latter have, through advertisement and propaganda, focused on teaching consumers about the enjoyable aspects of these technologies while leaving out the inconvenient aspects about their conflict with human rights.
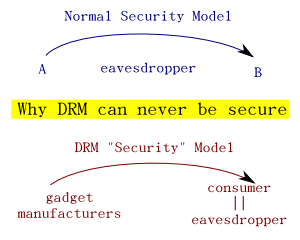 In fact the majority of
the ICT professors may have even given up their academic integrity by
remaining silent to the DRM scam artists' global-scale endeavors. In
a normal security model, the information flowing from A to B is
assumed to be exposed to the interception of eavesdroppers. An
important rule "Kerckhoffs' principle" states that a cryptosystem
should be secure even if everything about the system, except the key,
is public knowledge. Yet the DRM "security model" treats the receiver
of the information (the consumer) as one and the same as the
eavesdropper. This necessarily requires the DRM system to give up the
Kerckhoffs' principle, thereby rendering it breakable regardless of
the technology it employs.
(g: "Kerckhoffs drm" and "obscurity drm")
In fact the majority of
the ICT professors may have even given up their academic integrity by
remaining silent to the DRM scam artists' global-scale endeavors. In
a normal security model, the information flowing from A to B is
assumed to be exposed to the interception of eavesdroppers. An
important rule "Kerckhoffs' principle" states that a cryptosystem
should be secure even if everything about the system, except the key,
is public knowledge. Yet the DRM "security model" treats the receiver
of the information (the consumer) as one and the same as the
eavesdropper. This necessarily requires the DRM system to give up the
Kerckhoffs' principle, thereby rendering it breakable regardless of
the technology it employs.
(g: "Kerckhoffs drm" and "obscurity drm")
In non-technical terms, the DRM supporters know that the system is destined to be broken and yet they mislead the copyright holders to believe that their work can be "protected" by DRM. The ICT professors largely remain silent. To save their destined embarrassment, the DRM supporters went along to pressure the USA government to pass human-right-invading laws such as DMCA (Digital Millennium Copyright Act), and then to force its variants in the form of ACTA (Anti-Counterfeiting Trade Agreement) upon other governments. (g: "eff dmca" and "acta secret") The net effect is that these broken technologies along with their supporting laws can be used by these ICT companies to play the role of the Big Brother in George Orwell's dystopia "1984" (only more efficiently), to censor speech for example, while failing to deliver their promise of copyright protection.
We as a free society have to challenge this trend of erosion if we care about privacy, physical property right, freedom of speech, and other human rights in general. All this happens due to lack of public awareness. Interestingly, the best tool we have against this suffocating trend also happens to be an ICT artifact -- the Internet. By disseminating online (and offline) the above stories, facts, and search keywords, we can bring the public to be aware of what basic rights they are giving up as they purchase DRM-infected technologies. By disseminating online (and offline) the ideas about creative commons, free culture, and attention economy (each of which requires at least an entire article to discuss), we can bring the public to be aware of the new possibilities and benefits for the society as well as for each individual writer/artist/creator if s/he chooses to share her/his creative works with the world instead of guarding them as "intellectual properties". Hopefully we can not only stop the erosion of human rights but also empower digital consumers to take advantage of the read-write nature of the web 2.0 world, becoming an informed, dignified, and influential prosumer.
* Note: 'g: "abc xyz" ' means 'please google "abc xyz" (without the quotes)'.
![[rss feed 圖案]](/~ckhung/i/rss.png)
Comments
If you want a real scare to add to '1984', read 'Service Call' by Philip K Dick. In his 'The Collected Stories of--' he says that he never feared a gigantic monster-machine destroying mankind, but rather the machines we choose to surround ourselves with turning on us.
This post's comments feed